16 Malicious Browser Extensions Caught Stealing ChatGPT Credentials
Security researchers have discovered 16 malicious browser extensions targeting ChatGPT users across Chrome and Edge, capable of harvesting login credentials and session tokens. The campaign highlights a critical vulnerability in how users install and trust browser add-ons.
The Credential Theft Campaign Exposes Browser Extension Vulnerabilities
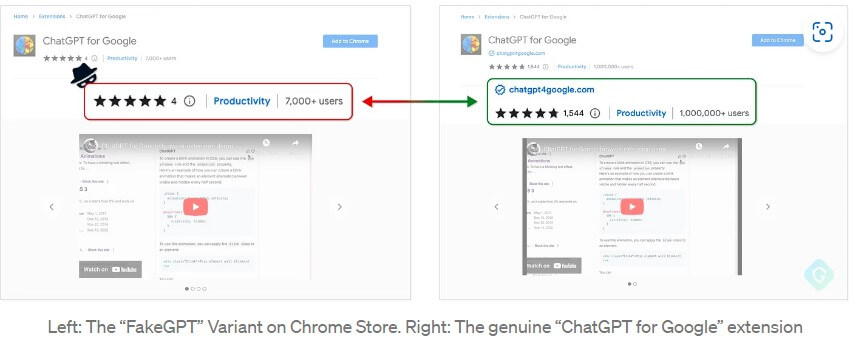
The battle for user trust in AI tools just got uglier. Researchers have uncovered 16 malicious browser extensions distributed across official app stores, specifically engineered to intercept ChatGPT login credentials and session tokens from unsuspecting users. This discovery underscores a persistent weakness in how major platforms vet third-party extensions before making them available to millions.
The extensions, masquerading as legitimate ChatGPT productivity tools, were designed to steal authentication data the moment users logged into their accounts. According to Bitdefender's analysis, these fake extensions employed sophisticated credential harvesting techniques that bypassed basic security checks. Once compromised, attackers could access ChatGPT accounts without triggering multi-factor authentication alerts, potentially exposing sensitive conversations and proprietary information.
How the Attack Works
The malicious extensions operated through a deceptively simple mechanism:
- Installation via official stores: Extensions were uploaded to Chrome Web Store and Microsoft Edge Add-ons, lending them false legitimacy
- Credential interception: Upon login, the extensions captured username, password, and session tokens in real-time
- Silent exfiltration: Data was transmitted to attacker-controlled servers without user notification
- Session hijacking: Stolen tokens allowed attackers to impersonate users and access accounts remotely
The Hacker News reported that some variants of these extensions also monitored user activity within ChatGPT, logging conversations and API interactions. This capability transformed the attack from simple credential theft into comprehensive account surveillance.
The Broader Threat Landscape
This incident is not isolated. Security researchers have documented a pattern of malicious Chrome and Edge extensions targeting AI platform users over the past year. Another investigation revealed extensions tied to the "DarkSpectre" campaign that affected millions of users globally, stealing not just ChatGPT credentials but also banking information and cryptocurrency wallet data.
The GhostPoster campaign demonstrated how attackers could weaponize browser extensions to conduct large-scale phishing operations and credential harvesting at scale. Additional research from Varonis identified the "Stanley" malware kit, which specifically targeted browser extension distribution as a vector for deploying credential-stealing malware.
Why Users Remain Vulnerable
The fundamental problem lies in the trust model of app stores. CyberScoop's investigation found that many users install extensions based solely on download counts and star ratings, without reviewing permissions or developer credentials. Attackers exploit this by creating convincing fake profiles and gradually building credibility before deploying malicious code.
Security experts warn that browser extensions remain a blind spot in most users' security awareness. Unlike traditional malware, extensions operate with explicit permissions to monitor web traffic, access passwords, and intercept data—making them ideal vehicles for sophisticated attacks.
Recommendations for Users and Organizations
- Verify developer identity: Only install extensions from official ChatGPT or reputable vendors
- Audit permissions: Review what data each extension can access before installation
- Use official apps: Prefer native applications over browser extensions where possible
- Monitor account activity: Regularly check ChatGPT login history for unauthorized access
- Enable 2FA: Activate two-factor authentication to prevent account takeover even if credentials are compromised
The discovery of these 16 extensions serves as a stark reminder that the convenience of browser extensions comes with significant security trade-offs. Until app store vetting processes improve, users must remain vigilant about what they install.



