China's OpenClaw Crackdown: What Practitioners Need to Know About Patent and Security Risks
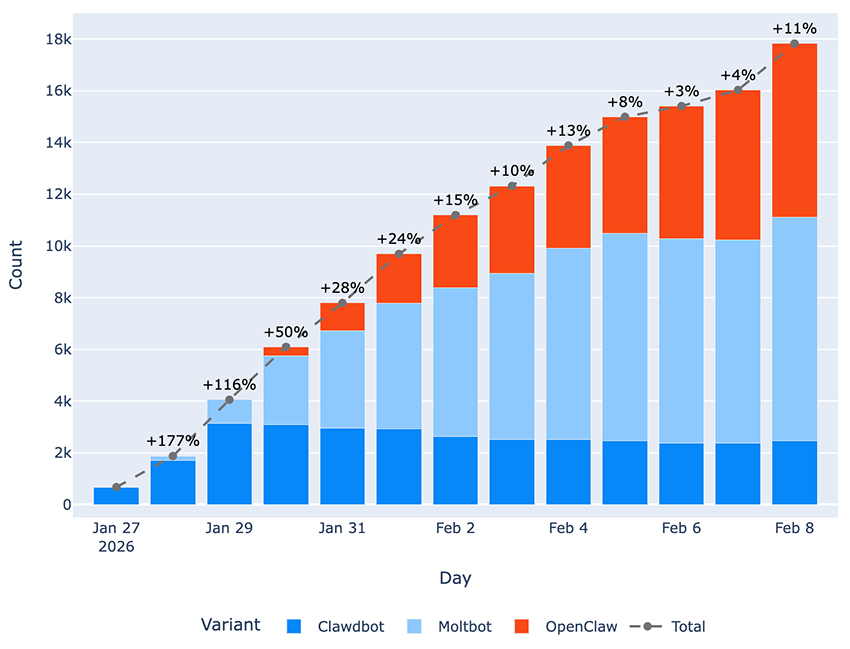
China has issued critical warnings about OpenClaw AI tool vulnerabilities, citing patent disputes and escalating security risks. Practitioners face new compliance challenges as adoption surges despite government restrictions.
The OpenClaw Security Reckoning
The race to deploy AI agents at scale just hit a regulatory wall. China's government has issued a formal warning about OpenClaw, flagging critical vulnerabilities that threaten both intellectual property and data security. What started as a promising open-source initiative for building autonomous AI systems is now facing intense scrutiny—and practitioners deploying OpenClaw in production environments need to understand the implications.
The warning comes as adoption of OpenClaw continues to surge across Chinese enterprises, creating a tension between innovation velocity and security governance. This isn't just regulatory theater: the risks are real, and the compliance landscape is shifting rapidly.
What's Actually at Risk
The core concerns center on two fronts:
Patent Vulnerability: OpenClaw's architecture may infringe on existing AI patents, creating legal exposure for organizations using the tool in commercial applications. This is particularly acute for state-sector deployments, where China has already begun restricting OpenClaw use.
Security Exposure: The tool's distributed agent architecture creates multiple attack surfaces. Exposed instances can leak training data, model weights, and proprietary prompts—a critical concern for enterprises handling sensitive workloads.
Practitioner Implications
For teams currently using or evaluating OpenClaw, the practical questions are straightforward:
- Compliance audits: If you're operating in China or serving Chinese customers, you need to assess whether OpenClaw deployments violate government restrictions.
- IP due diligence: Conduct patent landscape reviews before scaling OpenClaw in production, particularly for regulated industries.
- Security hardening: If you're continuing with OpenClaw, implement network isolation, access controls, and audit logging for all agent instances.
- Alternative evaluation: Consider whether competing frameworks (LangChain, AutoGen, or proprietary solutions) offer better security postures for your use case.
The Broader Context
The OpenClaw situation reflects deeper tensions in China's AI strategy. The government wants to foster innovation and open-source development, but it also needs to protect domestic IP and maintain security standards. OpenClaw became a test case—and it's failing that test.
For practitioners, this is a reminder that open-source tooling, while powerful, carries regulatory and legal risks that must be factored into architecture decisions. The speed of adoption often outpaces security hardening and legal review.
Moving Forward
Organizations with OpenClaw deployments should:
- Inventory current usage: Map all OpenClaw instances across your infrastructure
- Risk assessment: Evaluate exposure based on data sensitivity and geographic deployment
- Remediation planning: Develop timelines for migration or hardening
- Vendor communication: Engage with OpenClaw maintainers on security roadmap and patent resolution
The warning signals a maturing AI ecosystem where governance catches up to innovation. That's healthy long-term, but it creates near-term friction for practitioners who've already invested in OpenClaw integration.



