Databricks Investigates TeamPCP Supply Chain Breach: What We Know
Databricks is investigating a security breach connected to the TeamPCP supply chain campaign, raising critical questions about vulnerabilities in enterprise development tools and CI/CD pipelines.
The Supply Chain Attack Landscape Just Got Darker
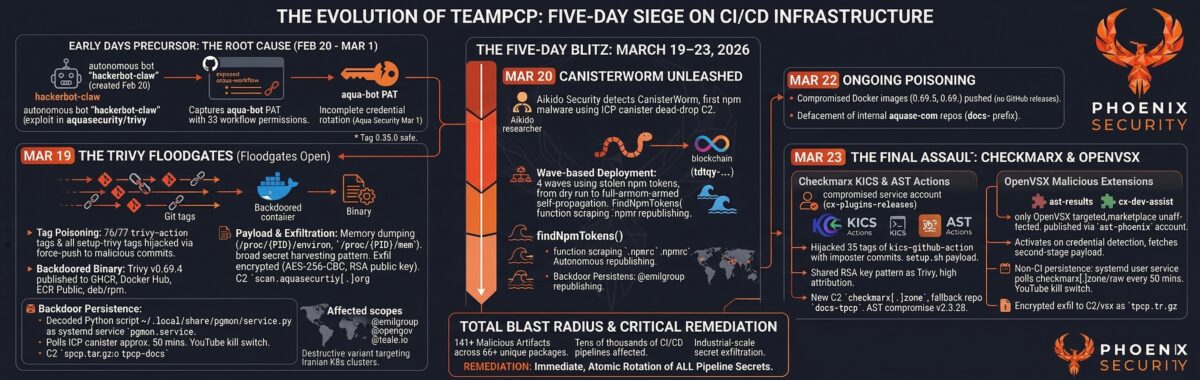
The battle for enterprise infrastructure security just shifted. Databricks is investigating an alleged compromise linked to the TeamPCP supply chain campaign, according to security researchers tracking the sophisticated attack operation. This development underscores a troubling trend: threat actors are systematically targeting the tools developers trust most—security scanners, package managers, and CI/CD platforms—to inject malicious code at scale.
Understanding TeamPCP's Attack Vector
TeamPCP is not a typical ransomware gang. According to security analysis, the campaign has compromised multiple critical infrastructure points in the software development pipeline, including vulnerability scanning tools and npm package repositories. The group's methodology reveals a calculated approach:
- Multi-stage infection: Attackers compromise legitimate development tools, then use them to distribute malware downstream
- Dual operations: TeamPCP simultaneously runs ransomware operations while conducting data exfiltration campaigns
- High-value targets: The group has already released sensitive data from major organizations, including pharmaceutical companies
The Databricks investigation suggests the attackers may have gained access to the platform itself, potentially affecting thousands of organizations that rely on Databricks for data analytics and machine learning workloads.
The Broader Supply Chain Context
This breach doesn't exist in isolation. The npm ecosystem has faced repeated supply chain attacks, including the CanisterWorm malware campaign that targeted package repositories. Similarly, other critical infrastructure has been compromised through poisoned development pipelines, demonstrating that TeamPCP is part of a larger ecosystem of sophisticated threat actors exploiting the trust placed in development tools.
What This Means for Enterprise Security
The Databricks investigation highlights critical vulnerabilities in how organizations secure their development infrastructure:
Immediate Concerns:
- Organizations using Databricks may have been exposed to malicious code injection
- The compromise could affect data pipelines processing sensitive information
- Supply chain attacks of this nature are notoriously difficult to detect and remediate
Broader Implications:
- Security scanners themselves have become attack vectors
- Traditional perimeter defenses are insufficient for protecting development environments
- Organizations need visibility across their entire software supply chain, not just application code
What Organizations Should Do Now
Security teams should prioritize immediate actions:
- Audit Databricks access logs for suspicious activity during the suspected compromise window
- Review dependencies in data pipelines for unexpected changes or new packages
- Implement supply chain security controls including SBOM (Software Bill of Materials) generation and verification
- Monitor for indicators of compromise related to TeamPCP's known infrastructure
The Ongoing Investigation
Databricks' investigation into the alleged compromise is ongoing, with security researchers continuing to track TeamPCP's activities. The group's demonstrated capability to compromise multiple points in the software supply chain—from development tools to package repositories—suggests this is not an isolated incident but part of a coordinated campaign targeting enterprise infrastructure.
As organizations increasingly rely on cloud-native development platforms and open-source ecosystems, the security posture of these tools becomes a critical enterprise risk. The Databricks investigation serves as a stark reminder that supply chain security is no longer optional—it's essential.



