Google Escalates Quantum Encryption Push as Threat Timeline Compresses
Google is sounding the alarm on quantum computing threats, pushing for immediate encryption overhaul. The tech giant warns that post-quantum cryptography must move from research to mandatory policy—before quantum machines can crack current security standards.
The Quantum Reckoning Is Here
The cryptographic foundations protecting everything from banking systems to government secrets face an existential threat—and the timeline for action is shrinking fast. Google is warning that quantum computing threats are now imminent, urging organizations to abandon outdated encryption standards before adversaries with quantum capabilities can retroactively decrypt sensitive data collected today.
This isn't theoretical anymore. Google is calling for a quantum security overhaul amid rising threats, signaling that the window for gradual migration has closed. The company's latest push represents a critical inflection point: post-quantum cryptography is shifting from research laboratories into mandatory government and industry policy.
From R&D to Regulatory Mandate
The stakes have fundamentally changed. Google is shifting post-quantum encryption from R&D to government policy mandate, recognizing that voluntary adoption moves too slowly when quantum threats loom. This pivot reflects a hard reality: organizations won't prioritize cryptographic overhauls without regulatory pressure.
The urgency stems from a specific vulnerability: harvest now, decrypt later attacks. Adversaries are already collecting encrypted communications with the assumption that quantum computers will eventually break current encryption. Any data protected by RSA-2048 or similar standards today becomes vulnerable once sufficiently powerful quantum systems emerge.
Key Drivers of the Quantum Threat
- Timeline compression: Quantum computers capable of breaking current encryption may arrive sooner than previously estimated
- Retroactive decryption risk: Data encrypted today can be stored and decrypted once quantum capabilities mature
- Legacy infrastructure: Most organizations still rely on cryptographic standards vulnerable to quantum attacks
- Supply chain exposure: Critical infrastructure, financial systems, and government networks all face synchronized vulnerability
The Cybersecurity Landscape Under Pressure
The broader cybersecurity ecosystem is already straining under existing threats. The fraud epidemic is testing the limits of cybersecurity, and quantum threats represent an additional layer of complexity that organizations must address while managing current attack vectors.
Preparing for a quantum future requires systematic preparation. Organizations should focus on three ways to prepare for a quantum future: inventory current cryptographic assets, develop migration roadmaps, and begin pilot implementations of post-quantum algorithms.
Building Quantum Readiness
Government and industry bodies are establishing frameworks for quantum preparedness. CERT-IN's quantum cyber readiness roadmap outlines structured approaches to assessing organizational vulnerability and implementing quantum-resistant cryptography at scale.
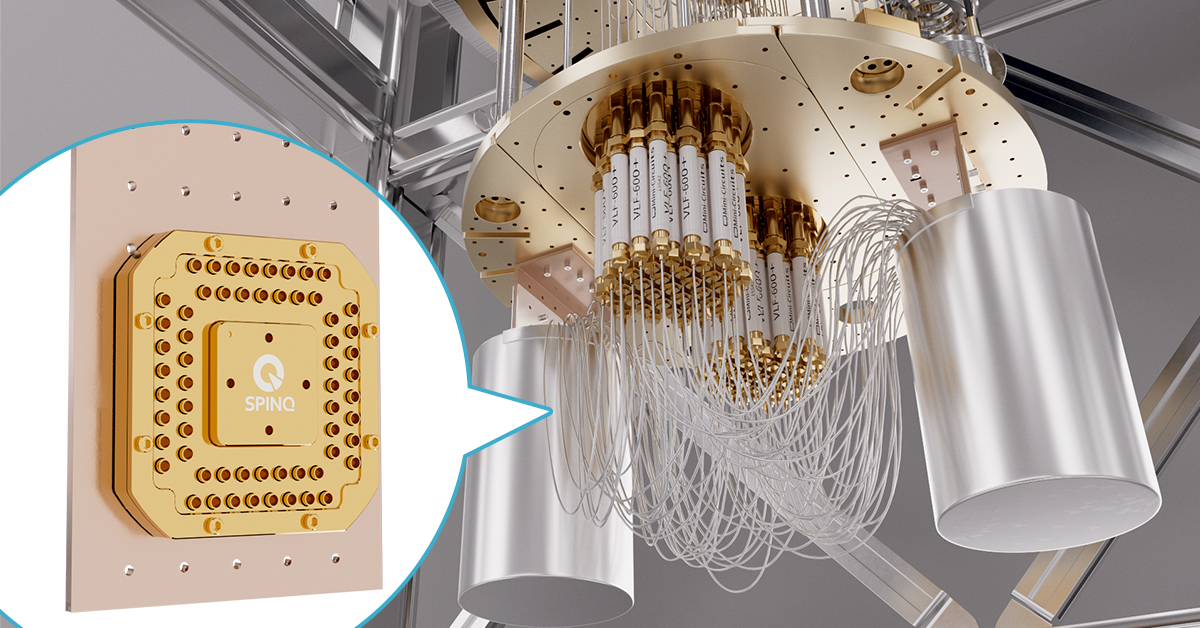
The technical challenge is substantial but solvable. Quantum-based platforms are staging the future of quantum computing, with researchers advancing both quantum hardware and the cryptographic defenses needed to counter it. Organizations that begin migration now—adopting NIST-standardized post-quantum algorithms—will establish resilience before the threat fully materializes.
The Competitive Imperative
Google's escalation signals that quantum security is becoming a competitive differentiator. Organizations that move first on post-quantum cryptography will gain regulatory approval, customer trust, and operational resilience. Those that delay risk catastrophic exposure.
The message is clear: quantum threats are no longer a future concern. They're a present-day imperative demanding immediate action.



